Ledger Recover Technical Whitepaper Released
Although a welcome move, the technical whitepaper has failed to alleviate the key concerns surrounding the upcoming recover service, whose source code is said to be released this summer.

- "Today, we are publishing the Ledger Recover White Paper, a key step in allowing anyone to audit the cryptographic protocols."
- In this white paper, you will find thorough coverage of Ledger Recover’s system design, the cryptographic protocol design and security goals, as well as details on the three primary operational flows:
- Backing up your Secret Recovery Phrase
- Restoring it on a new Ledger device
- Securely deleting your backups - "The main takeaway from the White Paper? Our upcoming service to be launched in Q4 2023, Ledger Recover, provided by Coincover, is 100% secure, and you can learn precisely how it works technically and examine the service yourself," said Ledger's CTO Charles Guillemet.
- "We encourage developers, researchers, and crypto-enthusiasts alike to look into this White Paper and fully understand Ledger Recover’s secure mechanisms," added the CTO.
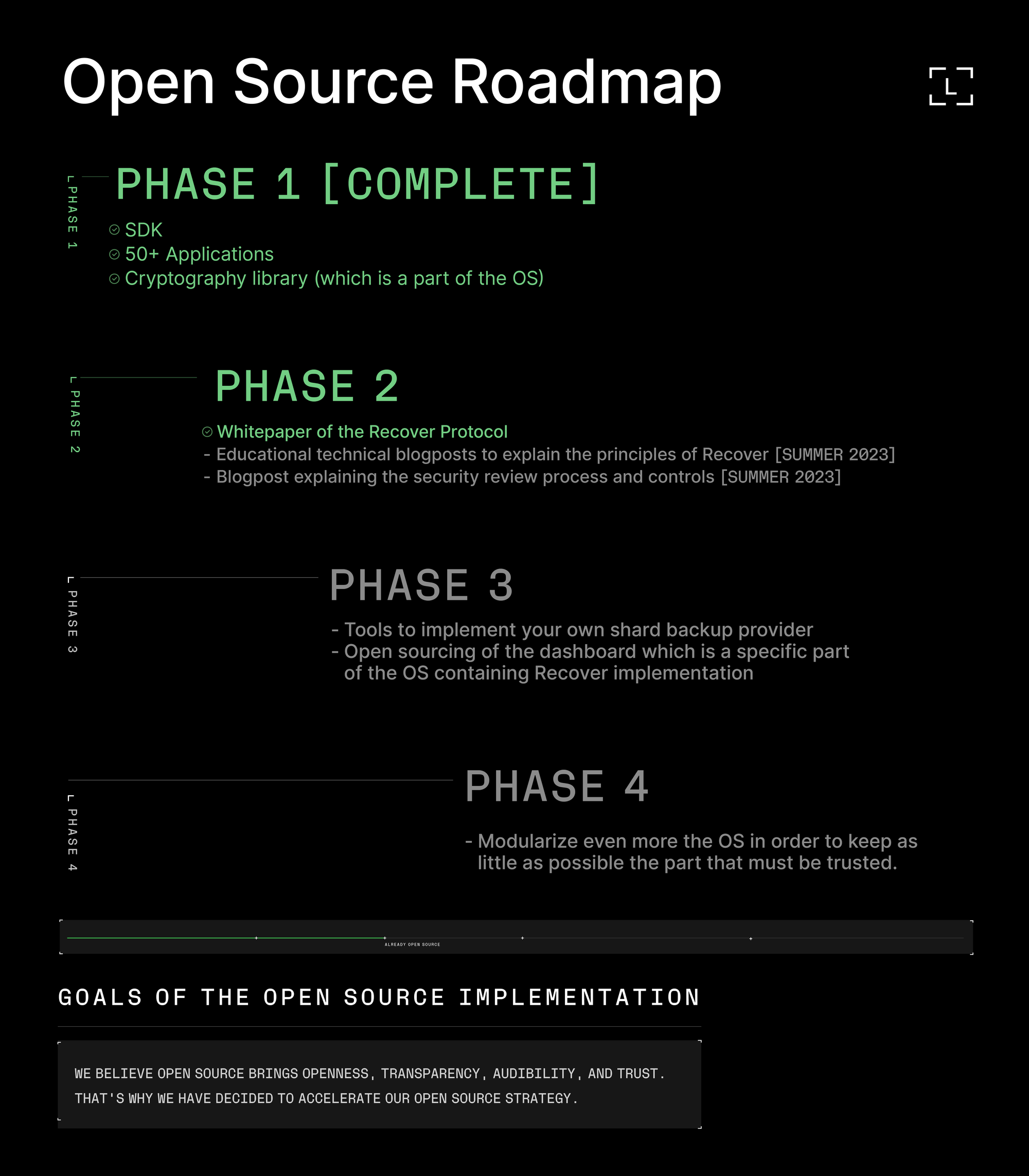
- In addition to the technical whitepaper of the cryptographic protocol, the company promised to release the source code of Ledger Recover this summer.
Some users already shared their initial thoughts.
- Seth For Privacy said "it confirms it's as bad as we thought, and still completely unverifiable in practice," and wrote a thread about it here.
"The bombshell here is the explicit confirmation that *Ledger themselves* hold the master decryption key for *all Ledger Recover users*. Your seed is encrypted using their key and not your own, so they always hold the ability to decrypt your seed from shards," he added.
- "Ledger Recover sounds like a disaster for the AI deepfake era. From my reading of their white paper, all an attacker needs to do is (1) get a photo of your ID and (2) know what you look like. No other verification needed. What are they thinking?!" wrote Zach Herbert of Foundation Devices.
Whitepaper Link / Archive
Blog Post / Archive
CTO Thread / Archive
GitHub Repo




