DoS: Fake Lightning Channels
"In my experiments, I was able to create hundreds of thousands of fake channels against victim nodes (owned by me), with all kinds of adverse effects. In some cases, funds were clearly at risk of being stolen due to the victim node’s inability to respond to cheating attempts," Matt Morehouse wrote.

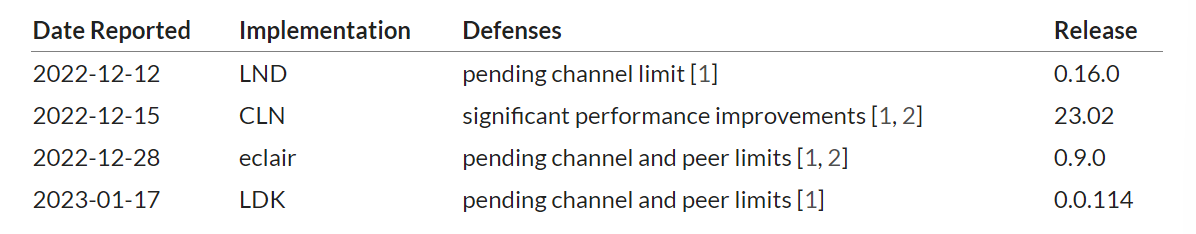
- Lightning nodes released prior to the following versions are susceptible to a DoS attack involving the creation of large numbers of fake channels:
- LND 0.16.0
- CLN 23.02
- eclair 0.9.0
- LDK 0.0.114
- "If you are running node software older than this, your funds may be at risk! Update to at least the above versions to help protect your node."
- "I reported the DoS vector to the 4 major lightning implementations around the start of 2023. All implementations have now shipped releases with defenses against the DoS."
- "Fake channels are trivial to create. Since there is no way for the victim to verify the funding outpoint sent to them in the
funding_createdmessage, the attacker doesn’t even need to construct a real funding transaction."
"An attacker can thus force a victim node to consume a small amount of resources by opening a fake channel with the victim and never publishing it onchain. If the attacker can create lots of fake channels, they can lock up lots of the victim’s resources."
Takeaways
- Use watchtowers. "When all else fails, watchtowers help to protect funds if your lightning node is incapacitated by a DoS attack. If you have significant funds at risk, it’s cheap insurance to run a private watchtower on a separate machine."
- Multiprocess architectures in general provide some defense against DoS.
- More security auditing needed. "The fact that this DoS vector went unnoticed since the beginning of the Lightning Network should make everyone a little scared. If a newcomer like me could discover this vulnerability in a couple months, there are probably many other vulnerabilities in the Lightning Network waiting to be found and exploited."




